How To Protect Your Account By Using Two Factor Authentication (2FA)?
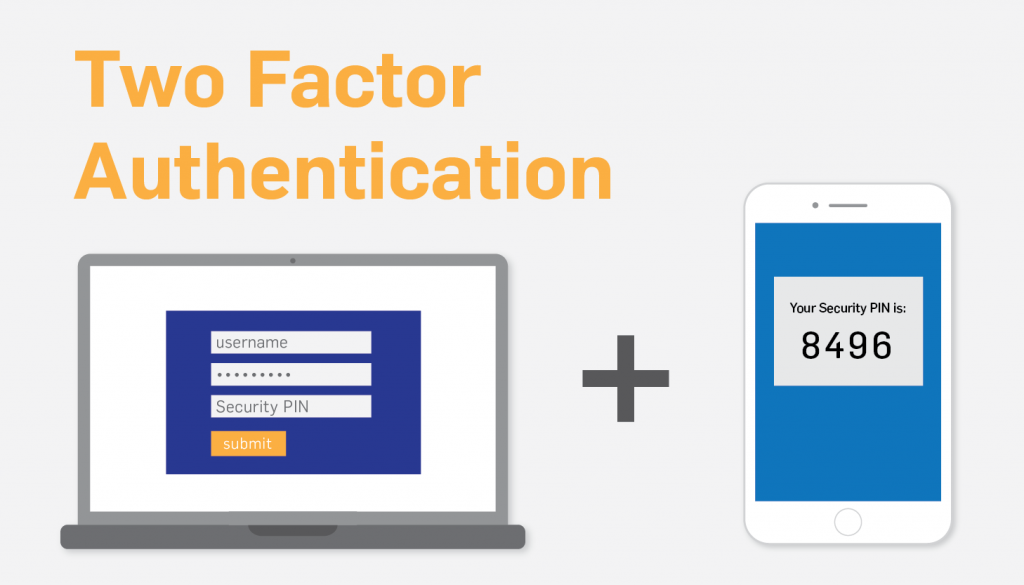
In this article, you will understand how to protect your account by using two factor authentication. You can easily increase the security of your online accounts by enabling two factor authentication. In simple words two factor authentication is two-step verification or dual-factor authentication this is an extra step added to gain access to an account for the security of your account and to verify the digital identity of the user.
This is the best way to protect the sensitive data of users and prevent any security threat like phishing, brute-force attacks, or social engineering. In this process, there are multiple factors not only based on username and password. In this article, we will tell you how to protect your account by using two factor authentication.
Factors of 2FA Authentication
As we already know the first factor is password and username and now we discuss the other factors of 2FA. Each factor stands for a sort of security control. There are 5 authentication factors.
- Knowledge Factor
The knowledge factor is the most used factor that verifies identities by providing some data or information that the user only accesses. Such as a password or personal identification number is used to authenticate that the username or email address is accessed by the authentic user.
- Inherence Factor
The inherence factor verifies the identity by using personal characteristics that would only belong to the user. The biometric one is the most common method for inherence authentication today, such as a fingerprint or thumbprint. also include voice and facial recognition, and iris scan. Inherence, authentication users have to be physically there.
- Time Factor
The time factor of authentication is based on the speculation of users logging time into a work computer. If someone is trying to attempt login or access a platform in an unusual time range the attempt will be unsuccessful to access a platform.
- Possession Factor
The possession factor of authentication verifies the identity of the user by a specific piece of information that is only possessed by the user. This factor is controlled through a device that belongs to the correct user such as memory cards and smart card tokens. Here is the process for the possession factor of authentication.
- At the time of registration, the user registers an account with a password.
- Using the username and password users login into their account.
- OTP is generated on the user’s mobile phone number while the user wants to access the system.
- After entering OTP the user gains access to the system.
- Location Factor
The location factor of authentication verifies the location around the world based on the user’s location. For example, the user had registered an account in one country and all of a sudden login attempts to another country. This factor verifies the identity of the user.
Importance of Two Factor Authentication (2FA)
In today’s world where digital crime and internet fraud increase the importance of two factor Authentication has been required. Recently highlighted security-related problems are password security breaches for DropBox and iCloud photo leaks. 2FA authentication makes it twice as a difficult stealing act of your information.
The fundamental element of a null trust security mode is known as two factor authentication. To protect sensitive data, you must confirm that users trying to access that data are what they say they are. 2FA is a powerful way to protect against multiple security threats such as brute-force attacks, social engineering, and more.
Here are some facts that needed to be more attention about traditional security practices.
- The same passwords use everywhere by two-thirds of people.
- After being scammed 57% of people still have not changed their password.
- Less than in six hours 91% of passwords will be cracked.
Two Factor Authentication (2FA): How does it work
2FA enhances your security by asking you to verify your identity through something you own (or hand over), such as your smartphone. This adds a security step when you log in to an online account in addition to your normal username and password. This can be done by sending an OTP to your smartphone. You are then asked to use this code to log in to your account. You can download an Authenticator app on your mobile device to help log in to specific online accounts and services as well. There is the whole process of two-step verification given below.
- The user login by website or application.
- The user enters a username and password then the server recognizes the user.
- The website generates a unique code for this process you do have not to require a password and username.
- After entering a unique code users have to provide pieces of information that only users have like biometrics and mobile device.
- Users have to enter OTP on their personal devices.
- After recognizing both factors the user gets access to the website.
How to set up Two-Step verification on Gmail (Google Account)
Google protects users’ accounts by promoting enabling two-step verification. This means after entering a password user need to answer notification on the user’s mobile phone.
Here are some steps to set up two-step verification for google:
- Sign in to the Google account page.
- Click on the Security on the left side.
- Scroll down you will find signing into a Google account and there is an option of 2-Step verification you have to click on 2-Step verification.
- The next screen shows you each time you sign in to your account you will need your password and a verification code. At the bottom of the screen, there is a button for Get Started click on this button.
- Enter your Google account password.
- After entering the password you have to use your phone and enter your phone no. Below are two options for how you want to get codes by text message or by phone call.
- For more protection, you can also use show more options. You will see there are two options first one is Security Key and another one is Google Prompt.
- Assume you click on Security Key this page will show you advance protection and if you click on Google Prmopts first you have to enter the password and it securely sent the code to your mobile number.
- After entering your phone number you will receive a 6 Digit Code enter code.
- The last step is to click on the button Turn ON.
For security try Mighty PC Cleaner and download it
Did you know that our Mighty PC Cleaner app can also help with your privacy and security? Mighty PC Cleaner can remove temporary Internet files like passwords from your web browser, plus it can delete information about files and folders you have accessed while using some Windows applications. It can safely erase files from the hard drive on the computers you want to give or sell. At this point, we have not even mentioned how using Mighty PC Cleaner can speed up your computer! However, we would say that it has been proven and tested by a third-party software testing expert to optimize PCs. Why not download the free version of MightyPCCleaner today?
Last Line!
Now, you can protect your account by using two-factor authentication. This article helps you to understand the importance of Two- Factor authentication and how it works. If you are facing issues when you apply two-step authentication, then contact our Technical Support Team. They assist you and resolve your issues as soon as possible.